
Kaspersky research finds attacks against the building automation, oil and gas industries grew in the first half of 2020
Monday, September 28, 2020
According to Kaspersky research, over the first six months of 2020, the percent of systems attacked in the oil and gas as well as the building automation industries increased when compared to H1 and H2 2019. Growth in these sectors occurred as the percent of industrial control system (ICS) computers attacked in other industries declined as cybercriminals shifted their focus to distributing more targeted and focused threats.
Attacks against industrial organizations always carry the potential to be particularly devastating, both in terms of disruption to production and financial losses. In addition, attacks against industrial enterprises have become more targeted, organized by sophisticated threat actors with extensive resources whose goals may not just be financial gain but also cyberespionage.
This past winter, spring and early summer, the industries most prone to attacks were building automation and oil and gas. Attacks against the latter have the potential to be catastrophic given the massive financial losses already incurred as a result of the COVID-19 pandemic. The percentage of ICS computers on which malicious objects were blocked grew from 38% in H2 2019 to 39.9% in H1 2020 in the building automation industry and 36.3 to 37.8% in the oil and gas industry.
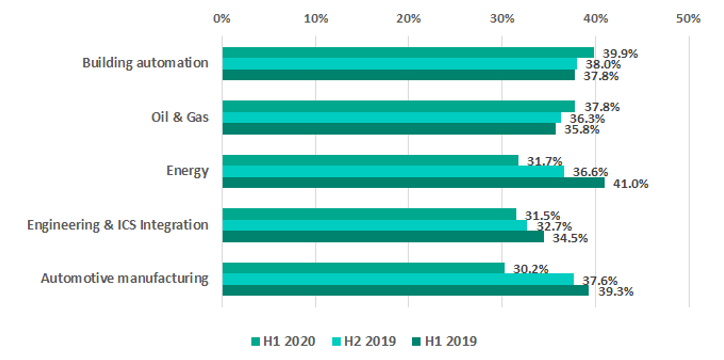
Percentage of ICS computers on which malicious objects were blocked in selected industries
Building automation systems tend to be more often exposed to attacks. They often have a larger attack surface than traditional ICS computers because they are frequently connected to corporate networks and the Internet. At the same time, because they traditionally belong to contractor organizations, these systems are not always managed by the organization’s corporate information security team, making them an easier target.
The growth percentage of ICS computers attacked in the oil and gas industry can be traced back to the development of a variety of worms (malicious programs that self-replicate on the infected device) written in script languages, specifically Python and PowerShell. These worms are able to gather authentication credentials from the memory of system processes using different versions of the Mimikatz utility. From the end of March to mid-June 2020, a large number of these worms were detected, primarily in China and the Middle East.
The increase in the percent of ICS systems attacked in the oil and gas and building automation industries was the exception for the first half of 2020, as the percent of systems attacked in most other industries declined. This occurred as attackers appeared to shift their focus from mass attacks to distributing more focused and targeted threats, including backdoors (dangerous Trojans that gain remote control over the infected device), spyware (malicious programs designed to steal data) and ransomware attacks (which tend to target specific enterprises). In fact, there were noticeably more families of backdoors and spyware built on the .NET platform that were detected and blocked on ICS computers. The percent of ICS computers affected by ransomware grew slightly in H1 2020 when compared to H2 2019 across all industries, with a series of attacks witnessed against medical facilities and industrial companies.
Industrial companies were also the victim of sophisticated campaigns by advanced persistent threat (APT) actors.
“The percent of ICS computers attacked across most industries is declining, however there are still threats to specific industries that are on the rise,” said Evgeny Goncharov, security expert at Kaspersky. “The more targeted and sophisticated attacks are, the greater potential they have to cause significant damage—even if they occur less frequently. What’s more, with many enterprises forced to work remotely and sign-in to corporate systems from home, ICS have naturally become more exposed to cyberthreats. With fewer on-sight personnel, there are fewer people available to respond and mitigate an attack, meaning the consequences may be far more devastating. Given that the oil and gas and building automation infrastructures appear to be a popular target among attackers, it’s crucial that these system owners and operators take extra security precautions.”
Learn more about the industrial threat landscape for H1 2020 on ICS CERT.
To keep your ICS computers protected from various threats, Kaspersky experts recommend:
- Regularly update operating systems and application software that are part of the enterprise’s industrial network. Apply security fixes and patches to ICS network equipment as soon as they are available.
- Conduct regular security audits of OT systems to identify and eliminate possible vulnerabilities.
- Use ICS network traffic monitoring, analysis and detection solutions for better protection from attacks potentially threatening technological process and main enterprise assets.
- Dedicated ICS security training for IT security teams and OT engineers is crucial to improve response to new and advanced malicious techniques.
- Provide the security team responsible for protecting industrial control systems with up-to-date threat intelligence. ICS Threat Intelligence Reporting service provides insights into current threats and attack vectors, as well as the most vulnerable elements in OT and industrial control systems and how to mitigate them.
- Use security solutions for OT endpoints and network such as Kaspersky Industrial CyberSecurity to ensure comprehensive protection for all industry critical systems.
- It is no less important to protect IT infrastructure as well. Integrated Endpoint Security protects corporate endpoints and enables automated threat detection and response capabilities.
About Kaspersky ICS CERT
Kaspersky Industrial Control Systems Cyber Emergency Response Team (Kaspersky ICS CERT) is a global project launched by Kaspersky in 2016 to coordinate the efforts of automation system vendors, industrial facility owners and operators, and IT security researchers to protect industrial enterprises from cyberattacks. Kaspersky ICS CERT devotes its efforts primarily to identifying potential and existing threats that target industrial automation systems and the Industrial Internet of Things. Kaspersky ICS CERT is an active member and partner of leading international organizations that develop recommendations on protecting industrial enterprises from cyberthreats. ics-cert.kaspersky.com
About Kaspersky
Kaspersky is a global cybersecurity company founded in 1997. Kaspersky’s deep threat intelligence and security expertise is constantly transforming into innovative security solutions and services to protect businesses, critical infrastructure, governments and consumers around the globe. The company’s comprehensive security portfolio includes leading endpoint protection and a number of specialized security solutions and services to fight sophisticated and evolving digital threats. Over 400 million users are protected by Kaspersky technologies and we help 270,000 corporate clients protect what matters most to them. Learn more at usa.kaspersky.com.
Additional Resources from Kaspersky
- 2/14/2022 - ATMs in the crosshairs: threats and defensive approaches
- 7/31/2019 - Financial Threats in H1 2019
- 6/18/2019 - Financial Cyberthreats in 2018
- Show All Kaspersky White Papers



























